Before You Outsource: The Internal Readiness Checklist for Software Teams
A fintech startup signed a six-month contract with an offshore development team. The team was qualified, and the vendor had good references. But three months in, they had almost nothing to show for it. It wasn’t because the developers were bad, but because the startup had handed them a half-page brief and hoped for the best.
They had no specs, technical reviewer, environment architecture, or coding standards. The outsourced team filled in every blank themselves, made reasonable assumptions, and built something the product team didn't want. By the time anyone caught it, the engagement was halfway through the budget.
The vendor wasn't the problem. The internal readiness was. That type of failure is far more common than a bad vendor choice.
TL;DR
Most outsourcing failures are internal, not vendor failures. Before you search for a partner, audit your own readiness: specs, technical oversight, environment architecture, repository controls, coding standards, and contracts. Missing any one of these will cost more time than the preparation would have taken. Two to four weeks of prep work prevents months of expensive rework.
The Outsourcing Readiness Problem Most Teams Skip
Most outsourcing guides start with how to find and evaluate vendors. That's the wrong starting point. The first question to answer is whether your organisation is ready to receive outsourced work effectively.
An outsourced team is only as good as the inputs you give them. They don't have years of context about your users, your architecture decisions, or the business logic buried in your codebase. They weren't in the room when you decided to use a particular data model or avoid a certain third-party dependency. Every gap in your documentation becomes a decision they make without you, and usually not the way you'd make it.
The common framing is that outsourcing risk is primarily a vendor selection problem. Find a better vendor, and your odds go up. While that's partly true, the more consistent predictor of a failed engagement is the client's internal readiness before the contract is signed.
The Internal Outsourcing Readiness Checklist
1. Do you have written specifications?
This is the single most important item on this list. A specification isn't a Confluence page with bullet points and a Figma link. It's a document that covers scope, acceptance criteria, technical constraints, edge cases, and what "done" means at every milestone, with enough detail that someone with no prior context on your business could build something you'd accept.
The test is simple: hand the spec to someone who doesn't know your product and ask them what questions they have. Every question they ask is a gap that the outsourced team will fill with an assumption.
A good spec for a backend feature typically includes: the data model being modified, the API contract (endpoints, request and response schemas, error codes), performance requirements, security constraints, existing tests the new code must not break, and a list of explicitly out-of-scope items. That level of detail is the difference between a first sprint that ships and one that produces a revision queue.
If you can't write a clear spec, you can't outsource the work. The time you'd spend explaining requirements, answering questions, and reviewing misaligned output is more than the time it takes to write the spec in the first place. Without written specifications, you're arguing over subjective impressions of quality with no reference point.
2. Do you have a technical reviewer?
You need at least one person on your side who can evaluate the outsourced team's output technically. Not someone who can approve a Jira ticket, but someone who can read the code, spot over-engineering, flag security issues, and make architectural calls with your interests in mind.
This doesn't have to be a full-time CTO. An engineer or technical product lead who spends a few hours a week on review is enough. What matters is that this person exists, is named before the engagement starts, and has clear authority to reject work that doesn't meet the bar.
Without a technical reviewer, you're accepting or rejecting work on faith. The same vendor that delivers excellent work under proper technical oversight will sometimes deliver over-engineered, high-billing solutions to a client with no reviewer. It isn’t intentional, but because there's no one to push back. There are documented cases of companies spending north of a million dollars on custom builds that off-the-shelf solutions would have handled adequately, because nobody on the client side had the standing to question the technical approach.
This reviewer also owns the code review process on your side. Every pull request from the outsourced team should pass through their queue before anything is promoted to staging. That review is your primary quality gate and your primary alignment mechanism throughout the engagement.
3. Is your environment architecture ready?
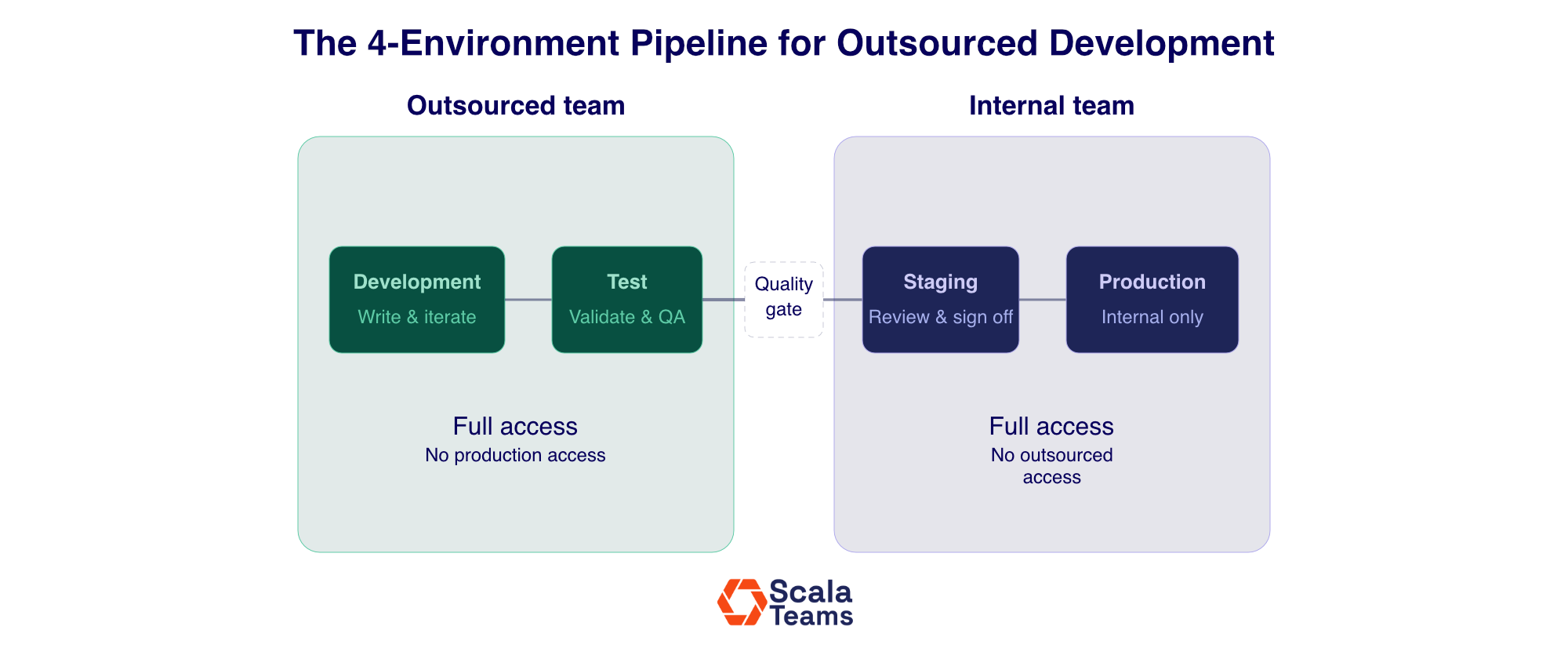
The outsourced team should never have access to your production environment. This is a structural foundation of a safe outsourcing relationship. Before work starts, you need a clear four-environment pipeline in place.
Development: Fully isolated. The outsourced team writes and iterates on code here. No production data, nothing live. They own this space day-to-day.
Test: Where automated and manual testing runs. The outsourced team validates their work here before it moves forward. Nothing advances until it passes their test suite.
Staging (pre-production): A mirror of production. Your internal team takes over here. Code that clears the test environment gets promoted to staging for your review and final validation before anything goes live.
Production: Your team only. The outsourced team never touches this environment.
This separation maintains a clean handoff point where your team validates work before it affects users and live data. Without it, a deployment error by an outsourced developer goes directly to production. With it, the worst case is a failed staging deploy that you catch before anyone outside your team is affected.
Setting up this four-environment architecture takes a few days for most teams. Retrofitting it after something goes wrong takes much longer. It typically happens under pressure, when speed matters most, and mistakes are most expensive.
4. Do you hold admin access to your repositories?
Every line of code the outsourced team writes should land in a repository where you are the administrator. The outsourced team gets contributor access. You control merges, branch protection rules, and access revocation.
This matters most at the end of an engagement. When it’s time to exit, you need to be able to remove access and keep your complete codebase intact. That's only possible if you held admin from day one. If the vendor holds repository ownership or co-admin rights, a contentious exit becomes significantly more complicated than it needs to be.
Also worth implementing: split sensitive components into separate repositories where possible. There's no reason a vendor building your front-end needs access to your core business logic, and no reason a vendor building a data pipeline needs access to your authentication service. Compartmentalisation limits exposure without limiting productivity; no single vendor holds the full picture of how your system works.
5. Do you have coding standards documented?
Coding standards are the shared definition of what acceptable work looks like in your codebase. Without them, every developer on the outsourced team writes to their own preferences.
The result isn't necessarily bad code. Sometimes it’s inconsistent code like different naming conventions across modules, test patterns that don't match, or error handling done three different ways in the same service. Your in-house team inherits a codebase that works but requires archaeology to extend, and the outsourced team is gone before the maintenance cost becomes fully visible.
Document your standards before the first sprint. At minimum: naming conventions, file and module structure, test coverage requirements and which testing frameworks to use, documentation expectations for public functions and non-obvious logic, and any patterns you explicitly prohibit. For Scala specifically, this also means decisions on functional style like immutability constraints, effect handling, and error model, because Scala gives developers enough freedom that two skilled engineers can write very different code for the same problem and both be technically correct.
6. Are your contracts ready to sign?
Don't wait until you've found a vendor you like to draft your contracts. Have your standard terms ready before the vendor conversation starts, and have them signed before any work begins.
At a minimum, your contracts need to cover four things:
IP ownership: Explicit work-for-hire language: all code produced under the engagement belongs to you.
Non-disclosure: Specific enough to cover your architecture, business logic, data models, and roadmap.
Milestone and deliverable definitions: Payment tied to specific, verifiable outcomes with clear acceptance criteria.
Termination rights: Reasonable notice periods and full codebase transfer as part of the handover protocol.
What "Not Ready" Actually Costs
Teams that outsource before they're ready don't fail catastrophically; they fail slowly. The first sprint produces something, but not quite right. Clarification rounds eat days. The review process is slow because nobody owns it on your side. Standards drift because they were never written down. By month two, the engagement is behind, over budget, or producing output that doesn't match what you imagined. Then, the frustration gets directed at the vendor when the problem was upstream the whole time.
The cost shows up in specific line items. Reworking misaligned outputs typically absorbs one to two sprints of lost velocity in the first month alone. Management overhead for a senior engineer who owns review but wasn't factored into the headcount model runs 15 to 20% of their working hours, ongoing. Environment setup and security incident response if access controls weren't established at the start: variable, but never cheap, and always urgent.
The preparation in this checklist takes two to four weeks for most teams. Writing the spec is the longest part. Everything else (environment setup, repository configuration, contract review, standards documentation) can run in parallel. That four-week investment compounds across every sprint of the engagement. A six-month contract entered at proper readiness produces reliably more usable output than the same contract entered prematurely, even accounting for a delay.
Getting Ready for Outsourcing in Stages
If you're not ready across all six areas, prioritize in this order: spec first, then technical reviewer, then environment architecture, then repository controls, then coding standards, then contracts. The first three are the ones that break engagements mid-flight. The last three determine how cleanly they end and how maintainable the codebase is after the vendor is gone.
Running this checklist is itself a useful exercise, independent of the result. Teams that work through it often discover that their requirements aren't as defined as they thought. They find that the translation from product intent to engineering specification hasn't been done yet. That gap would have caused problems with an in-house team, too. The checklist helps to identify issues when there's still time to fix them.
Once you've confirmed readiness, the next evaluation is whether the right organizational signals are in place to make outsourcing the correct decision at all (capacity gaps, specialist needs, hiring timeline pressure). That's a separate question worth running before the vendor search begins.
Scala Teams works with engineering leaders at the spec and architecture stage, not just at the point of hire. If you're evaluating an outsourced Scala engagement and want to pressure-test your readiness, talk to us about what that looks like in practice.